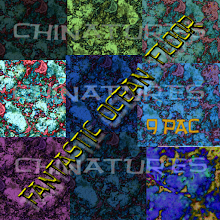
Yes it's my creation. Title: House of Cards. Now go away copyright police.
sapphoq reviews continues in a heated vein: And I will say it again. Deciding that people have to use their wallet names or the average-looking name that others "call you" on G+ or any other site is in my opinion, FAILBOAT. Regardless of the intentions of any service, there are activists whose lives are in danger because of censorship. Some of those activists may be using G+ as the platform that is still currently available in their country or via a proxy. Although there are many activists and other seriously oppressed people on Twitter, not everyone has the ability or inclination to par their message down to 140 words. When it comes to human rights violations, the idea is to get the message out to as broad an audience as possible.
I believe in my heart of hearts that all this hoopla over using our wallet names is so that Google's advertiser base can find us easier.
http://my.nameis.me/
http://techcrunch.com/2011/07/24/google-plus-has-a-problem-fear-not-i-have-a-solution/
https://www.eff.org/deeplinks/2011/07/case-pseudonyms
https://www.eff.org/deeplinks/2011/12/2011-review-nymwars
https://www.eff.org/deeplinks/2012/01/google-pseudonyms-step-right-direction-not-end-road
https://www.eff.org/deeplinks/2012/01/right-anonymity-matter-privacy
http://infotrope.net/2011/07/25/preliminary-results-of-my-survey-of-suspended-google-accounts/
http://liv.dreamwidth.org/354658.html
http://elf.dreamwidth.org/435804.html
http://geekfeminism.org/2011/07/08/anti-pseudonym-bingo/
http://metaverse.acidzen.org/2008/pseudonymity
http://metaverse.acidzen.org/2008/pseudonymity-internet
http://www.physorg.com/news66401288.html
http://disabledfeminists.com/2010/04/14/on-refusing-to-tell-you-my-name/
http://www.historiann.com/2009/07/31/an-object-lesson-in-pseudonymity-and-internet-privacy/
http://www.zdnet.com.au/googles-real-names-a-real-disaster-339321277.htm
https://disqus.com/research/pseudonyms/
https://www.eff.org/deeplinks/2011/08/randi-zuckerberg-runs-wrong-direction-pseudonymity
http://my.nameis.me/348/hisham-almiraat/
http://www.guardian.co.uk/science/punctuated-equilibrium/2011/jul/25/1
http://www.huffingtonpost.com/dawn-teo/famed-anonymous-anti-pali_b_180313.html
http://www.nationalreview.com/bench-memos/49962/exposing-irresponsible-anonymous-blogger/ed-whelan
http://obsidianwings.blogs.com/obsidian_wings/2009/06/stay-classy-ed-whelan.html
http://articles.nydailynews.com/2009-08-19/news/17933742_1_liskula-cohen-blogger-google
http://advocacy.globalvoicesonline.org/projects/guide/
http://www.talesfromthe.net/jon/?p=2918%23comment-179952
http://www.pcmag.com/article2/0,2817,2388640,00.asp
http://lauren.vortex.com/archive/000880.html
http://geekfeminism.wikia.com/wiki/Who_is_harmed_by_a_%22Real_Names%22_policy%3F
http://cityofnidus.blogspot.com/2011/07/google-and-future-of-avatar-identity.html
http://coffeeandink.livejournal.com/901816.html
http://kateharding.net/2007/04/14/on-being-a-no-name-blogger-using-her-real-name/
http://www.zephoria.org/thoughts/archives/2011/08/04/real-names.html
http://www.pcmag.com/article2/0,2817,2388626,00.asp
http://gomiso.blogspot.com/2011/07/g-and-beyond-whats-your-target.html
http://dwellonit.taterunino.net/2011/07/11/follow-up-google-confirms-real-names-a-requirement-for-profilesplus-mostly/
http://news.cnet.com/8301-13506_3-20059247-17.html